WEBORION® MONITOR
We notify you when your
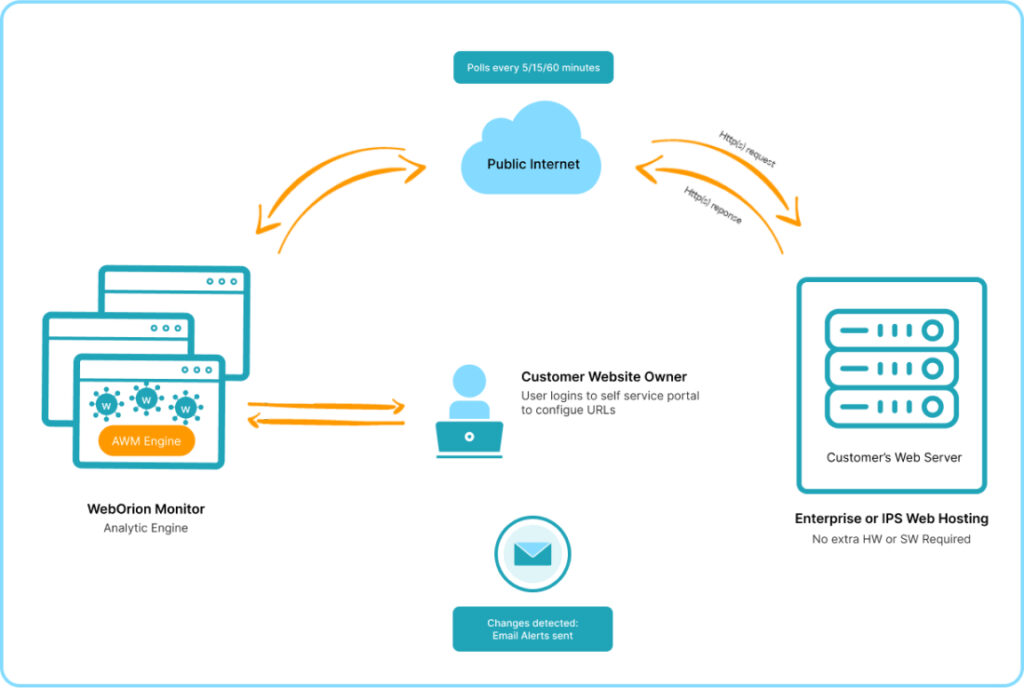
WebOrion® Monitor provides an instantaneous, agentless and continuous way to monitor all your websites for many hacks including defacements, tampering of HTTP headers, javascripts, TLS certificates and DNS/Whois changes. Our high-fidelity approach in monitoring your website, using our powerful and innovative engines, provides you with a high level of assurance and reliability.
know more
Comprehensive and AI-Powered Capabilities
Proactive 24x7 Agentless Monitoring
Our Monitor can be easily set up in minutes with no agent installation. It will proactively poll your webpage round the clock to give you greater assurance that your website’s confidentiality, integrity and reputation is intact in front of your customers and partners.
Platform Independent
Our Monitor supports websites hosted on-premise or in the cloud. We also support any web technology stack including popular Content Management System (CMS) such as WordPress, Joomla, and Drupal, Magnolia, Sitefinity, etc.
Automated with Integrated Response
Our Monitor can be integrated with our Restorer to provide a one-touch or automatic failover to a temporary Secure Replica to preserve your online presence and branding.
Our Unique Features and Engines
AI-Powered Plus Many More
Our advanced and configurable engines, with highly advanced AI option, are carefully designed to detect changes due to web defacement, malicious code, third-party Javascripts, malware, and more. Unique and Intelligent baseline process automatically differentiates dynamic and static parts of your website, allowing more effective web monitoring with minimal false alerts.

Content Analytics
Analyzes HTML source code (e.g. page title, links and frames) to determine if the webpage has been modified

Automate Integrity Analytics
Analyzes HTML source code (e.g. page title, links and frames) to determine if the webpage has been modified

Artificial Intelligence Engine
Our Unique AI Engine runs advanced Natural Language Processing (NLP) models that were trained from >10years

Image Analytics
Besides code and file checks, our Monitor also renders the webpage as an image to do advanced pixel analysis.

Javascript Malware Detection Engine
Our Malware Engine checks for the presence of well-known card skimming and cryptojacking javascripts

SSL/DNS/Whois Change Monitoring
Our Monitor tracks any changes to the DNS and Whois configurations of the website

Payment Page Monitoring
Our Monitor can be programmed to monitor important payment pages to prevent card-skimming attacks

HTTP Header Monitoring
Our Monitor will scan regularly for any change or tampering of the HTTP Headers. This includes checking for CSP and HTTP

SSL/DNS/Whois Change Monitoring
Our Monitor can also provide the continuous monitoring of the script inventory from inline, first, second, third and fourth party
lorem ipsum
The Best Defense is Good Cybersecurity
Tab One
Tab Two
Tab Three
Tab One
Tab Item One
Lorem ipsum dolor sit amet consectetur. Lectus nullam nisi malesuada et lobortis tellus hac. Pellentesque ullamcorper tempor convallis tortor. Accumsan tellus cras posuere
Tab Two
Tab Item Two
Lorem ipsum dolor sit amet consectetur. Lectus nullam nisi malesuada et lobortis tellus hac. Pellentesque ullamcorper tempor convallis tortor. Accumsan tellus cras posuere
Tab Three
Tab Item Three
Lorem ipsum dolor sit amet consectetur. Lectus nullam nisi malesuada et lobortis tellus hac. Pellentesque ullamcorper tempor convallis tortor. Accumsan tellus cras posuere
our enterprise
Flexible Deployment Models
Cloud SaaS Subscription
Fast and Easy Deployment
Near instantaneous on-boarding with a Cloud SaaS account
Highly scalable to support thousands of websites or URLs all over the world
Share hosting provides optimal costing and speed of deployment
Cloud VPC or On-Premise
Dedicated to your environment
Packaged as a virtual appliance that can operate as a virtual machine (VM) or docker container
Can be deployed in any VPC in your public cloud (including AWS, Azure, Google, Huawei, etc)
Provides data sovereignty and security settings customized to your environment
Monitoring Solution
High Level Network Architecture