
DNS – A Brief Summary of an Easily Overlooked System
As a website owner, one would surely come across the Domain Name Service (DNS). DNS is an extremely critical system on the Internet, as it is a system that helps translate domain names (which are easily recognisable and remembered) into IP addresses. It is important for all website owners to know and understand the DNS.
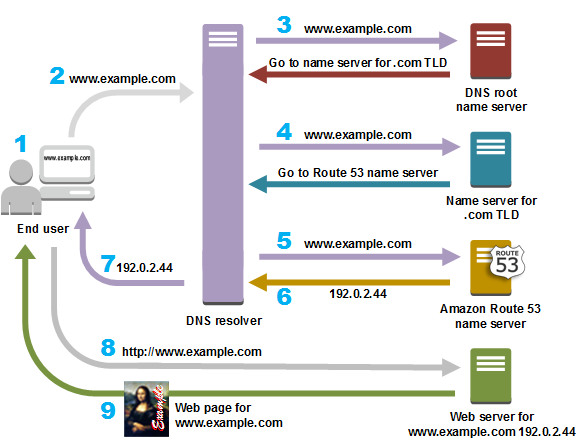
The graphic shown below (from Amazon) briefly illustrates the DNS structure and flow of information when a hostname is input (assuming Amazon Route 53 is used as the preferred DNS service).
Source: https://aws.amazon.com/route53/what-is-dns/
1. The DNS root name server in your DNS root zone is first contacted by your DNS recursor (or resolver). It returns the address of the server (responsible in your zone) containing the Top Level Domain (TLD). In this example, it is the .com TLD.
2. The .com TLD server is contacted by your DNS recursor. It returns the address of the authoritative nameserver for the domain entered. In this example, Amazon Route 53 is used as the authoritative nameserver (hence, its address is returned), while example.com is the domain desired.
3. The authoritative nameserver contains the DNS records in its local database, called the zone file. It usually hosts two zones for each domain:
- Forward Lookup Zone : Used to find the IP address of a specific hostname
- Reverse Lookup Zone : Used to find the hostname of a specific IP address.
These are used to resolve the DNS recursor’s queries, which returns the relevant information to your browser, eventually letting your browser know which IP address to contact when accessing www.example.com.
Types of DNS Records
There are many types of DNS records, stored and used based on context and relevancy. Common records include:
- NS : Nameserver records contain the name of the authoritative nameservers hosting the DNS records for a domain
- A : Address records contain the IP address of a hostname (e.g. www.example.com)
- CNAME : Canonical Name Records are aliases for other address records (e.g. www.example.com is an alias of example.com)
- MX : Mail exchange records contain the names of servers that handle emails for a domain.
- TXT : Text records contain arbitrary data and can be used for a wide variety of reasons (e.g. domain ownership verification)
DNS records contain a large amount of information, making it a target for malicious attackers to gather information about your web server.
Enumeration Tools
In the current age of modern computing, it is not difficult to find advanced, automated tools. In Kali Linux, there are two notable tools that can automate DNS enumeration (non-exhaustive):
- DNSRecon
- DNSenum
DNSRecon and DNSenum are both scripts that provide the ability to automate the process of enumerating DNS information of a domain. (You may refer to Kali Linux’s website to learn more about DNSRecon and DNSenum.) This makes it easier for any unsecured or public information to be displayed. Any information gathered is a point of interest to attackers who desire to compromise your web server.
As a web server owner or administrator, it is critical to protect your server from DNS related attacks by choosing a secure, reliable, reputable DNS service provider. Although not directly related to web administrators, NIST has released a publication concerning the secure deployment of DNS. Certain important pointers of a secure DNS service provider can be distilled from this publication, which you may use as points of comparison when choosing a DNS service provider:
- How have they secured their DNS hosting environment?
- How have they secured DNS transactions?
- How have they secured DNS queries and responses?
WebOrion SSL/DNS/Whois Monitoring
In the event that your DNS records have been compromised, WebOrion Monitor can also perform regular checks using its SSL/DNS/Whois Monitoring Engine. This allows WebOrion Monitor to regularly check for any changes to SSL, DNS, and whois configurations of the website. Any changes will cause alerts to be sent to the user. If you are interested, do drop us an email at sales@cloudsine.tech.
Stay safe!

